Spectre Meltdown
Spectre/Meltdown security vulnerability caused by flaws in processors and how to patch them
systemcheck might have referred you to this page.
Note:
- systemcheck is a diagnostic tool that automates the display of diagnostic output from other diagnostic tools.
- Kicksecure is not the cause of the issue. Don't kill the messenger.
- Spectre/Meltdown is a security vulnerability caused by flaws in hardware, specifically in CPUs (processors).
- This page explains the current state of affairs and how to protect against this security vulnerability.
Introduction
A CPU is not just a dumb piece of hardware that can do basic calculations at high speed. Modern CPUs from Intel and AMD have many "software-like" features built-in. To name a few from a plethora of examples:Open Source BIOS and Firmware Security Impact
Security issues have been discovered in CPUs.
One recent example of a firmware vulnerability is the processor microcode update for modern chips to address speculative![]() execution flaws
execution flaws![]() . [1]
. [1]
Platform Specific
Select your platform.
Host Operating System
If Kicksecure is run as a host operating system, then no further user action is required. This is because microcode packages are already installed by default, and security-misc applies hardened kernel settings that enable all available mitigations.
VirtualBox
There is no solution for VirtualBox yet. The bug has been reported to the VirtualBox developers. For bug report tickets and related forum discussions, see footnote. [2] The Kicksecure developers depend on the VirtualBox developers to fix this VirtualBox issue. Users must patiently wait for VirtualBox developers to fix this bug. Nevertheless:
- Apply Processor Microcode Updates on your host operating system. (Not required if using Kicksecure as the host operating system, as this is already done by default.)
- Consider the following experimental instructions.
Testers only! For more information, please click "expand" on the right.
- Check back later for updated instructions. Stay Tuned.
KVM
1. Processor Microcode Updates.
Apply Processor Microcode Updates on your host operating system. (Not required if using Kicksecure as the host operating system, as this is already done by default.)
The updated mitigative host CPU instructions are passed through by default.
2. Done.
No further action is needed.
Qubes
If Qubes is run as a host operating system, then no further user action is required. This is because microcode packages are already installed by default in Qubes. This is unspecific to Kicksecure. Therefore, for additional information, check with upstream Qubes directly as per the Self Support First Policy.
Documentation previously stated, see footnote. [11]
Processor Microcode Updates
Processor microcode is unfortunately non-freedom software, therefore only available in the Debian nonfree repository. [12] [13] Kicksecure recommends to avoid non-freedom software, but in this case, idealism would result in insecurity.
It is unnecessary to apply these updates in standard guest VMs, as they do not have the ability to alter the microcode. However, processor microcode updates should always be applied on the host operating system (for processors by Intel or AMD). [14] [15]
Microcode Package Check
If there is no output from the following checks, the package is not installed.
To check whether the microcode package is installed:
Debian-based
On the host, run:
Click = Copy Copied to clipboard!
Qubes
In dom0, run:
Click = Copy Copied to clipboard!
The Qubes check should confirm that the microcode_ctl.x86_64 package is already installed. [16]
Install Microcode Package
To install the microcode packages: [17]
Choose either Intel or AMD:
Intel
Install package(s) intel-microcode. Follow steps A to E.
A.
Update the package lists and upgrade the system
![]()
![]() .
.
Click = Copy Copied to clipboard!
B. Install the intel-microcode package(s).
Using apt command line
--no-install-recommends option
![]()
![]() is in most cases optional.
is in most cases optional.
Click = Copy Copied to clipboard!
C. Done.
The procedure of installing package(s) intel-microcode is complete.
AMD
Install package(s) amd64-microcode. Follow steps A to E.
A.
Update the package lists and upgrade the system
![]()
![]() .
.
Click = Copy Copied to clipboard!
B. Install the amd64-microcode package(s).
Using apt command line
--no-install-recommends option
![]()
![]() is in most cases optional.
is in most cases optional.
Click = Copy Copied to clipboard!
C. Done.
The procedure of installing package(s) amd64-microcode is complete.
spectre-meltdown-checker
It is possible to check if the system is vulnerable to the Spectre![]() and Meltdown
and Meltdown![]() attacks, which exploit flaws in modern chip design to bypass system protections.
attacks, which exploit flaws in modern chip design to bypass system protections.
Host versus VMs
Is spectre-meltdown-checker useful in VMs? Unreliable. [18]
spectre-meltdown-checker should be run on the host operating system.
Installation
Install package(s) spectre-meltdown-checker. Follow steps A to E.
A.
Update the package lists and upgrade the system
![]()
![]() .
.
Click = Copy Copied to clipboard!
B. Install the spectre-meltdown-checker package(s).
Using apt command line
--no-install-recommends option
![]()
![]() is in most cases optional.
is in most cases optional.
Click = Copy Copied to clipboard!
C. Done.
The procedure of installing package(s) spectre-meltdown-checker is complete.
Usage
Click = Copy Copied to clipboard!
Forum Discussion
See: https://forums.whonix.org/t/whonix-vulerable-due-to-missing-processor-microcode-packages/5739![]()
Leak Tests
Google's PoC is a Spectre V1 gadget that utilizes a JavaScript array speculatively accessed out of bounds. While the V1 gadget can be mitigated at the software level, Chrome's V8 team determined that mitigating other gadgets, such as those for Spectre Variant 4, is "simply infeasible in software." The code is designed for Intel Skylake CPUs but can potentially work on other architectures and browsers with minor modifications to the JavaScript. Google successfully ran this attack on Apple M1 ARM CPUs without any major changes. [19]
References
- ↑
https://www.debian.org/security/2018/dsa-4279

- ↑
- VirtualBox 5.2.18 vulnerable to spectre/meltdown despite microcode being installed (#17987)

- Request for VBox to pass through Speculative Store Bypass (SSB) mitigations to guest => duplicate of #17987 (#18477)
 ticket.
ticket. - the associated VirtualBox forum discussion

- a related Whonix forum discussion: Whonix vulnerable due to missing processor microcode packages? spectre / meltdown / retpoline / L1 Terminal Fault (L1TF)

- https://security.stackexchange.com/questions/211265/virtualbox-spectre-v4

- VirtualBox 5.2.18 vulnerable to spectre/meltdown despite microcode being installed (#17987)
- ↑
VirtualBox version
5.2.18or above is required, as only that version includes Spectre/Meltdown defenses. - ↑
--ibpb-on-vm-[enter|exit] on|off: Enables flushing of the indirect branch prediction buffers on every VM enter or exit respectively. This could be enabled by users overly worried about possible spectre attacks by the VM. Please note that these options may have severe impact on performance.
https://www.virtualbox.org/manual/ch08.html
There is a mistake in the VirtualBox manual stating
enterwhich does not work. It is actuallyentry. - ↑
https://www.virtualbox.org/manual/ch08.html

--l1d-flush-on-vm-enter on|off: Enables flushing of the level 1 data cache on VM enter. See Section 13.4.1, “CVE-2018-3646”.
- ↑
--l1d-flush-on-sched on|off: Enables flushing of the level 1 data cache on scheduling EMT for guest execution. See Section 13.4.1, “CVE-2018-3646”
 .
.
https://www.virtualbox.org/manual/ch08.html
- ↑
https://www.virtualbox.org/manual/ch13.html#sec-rec-cve-2018-3646

For users not concerned by this security issue, the default mitigation can be disabled using
Click = Copy Copied to clipboard!Since we want to enable the security feature we set
--l1d-flush-on-sched on. - ↑
--spec-ctrl on|off: This setting enables/disables exposing speculation control interfaces to the guest, provided they are available on the host. Depending on the host CPU and workload, enabling speculation control may significantly reduce performance.
https://www.virtualbox.org/manual/ch08.html
- ↑
According to this VirtualBox ticket

--spec-ctrlshould be set toon. - ↑
--nestedpaging on|off: If hardware virtualization is enabled, this additional setting enables or disables the use of the nested paging feature in the processor of your host system; see Section 10.7, “Nested paging and VPIDs” and Section 13.4.1, “CVE-2018-3646”.
- ↑
After getting all dom0 host upgrades
 and rebooting, this should be OK.
1. Launch a
and rebooting, this should be OK.
1. Launch a dom0terminal.
Click the Qubes App Launcher (blue/grey "Q")→Open the Terminal Emulator (Xfce Terminal)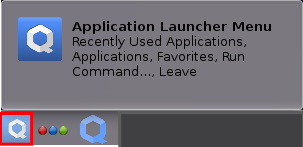 2. Upgrade Qubes
2. Upgrade Qubes dom0. This step is mandatory. Click = Copy Copied to clipboard! 3. Done. Thedom0upgrade has been completed. 4. Reboot. Click = Copy Copied to clipboard! - ↑
Relevant Debian packages for processor microcode: Intel
 and amd64
and amd64 .
.
- ↑
Installing these updates by default would require enabling the Debian
nonfreerepository, which would logically make Kicksecure images non-freedom. - ↑ ARM is less affected than Intel architecture.
- ↑
See: https://forums.whonix.org/t/whonix-vulerable-due-to-missing-processor-microcode-packages/5739

- ↑ This package is installed by default in Qubes to automatically protect users against hardware threats.
- ↑ Strictly speaking, installing the microcode package for your specific CPU (Intel or AMD) would suffice. However, Kicksecure installs both packages by default. The other package will not have any effect but is useful to have installed if migrating to another CPU vendor.
- ↑
https://github.com/QubesOS/qubes-issues/issues/4262#issuecomment-579388171

most automated tests we run are in virtualized environment (Qubes inside KVM) - results there will be even more unreliable.
spectre-meltdown-checker bug report: False positives inside Xen (PVH) domU

- ↑
https://www.phoronix.com/scan.php?page=news_item&px=Google-Leaky.Page-Spectre

<ref> tag defined in <references> has no name attribute.
We believe security software like Kicksecure needs to remain Open Source and independent. Would you help sustain and grow the project? Learn more about our 12 year success story and maybe DONATE!




















